
IT Support Impact Summary
Analyzed a real-world healthcare data breach to understand how everyday IT decisions such as access control handling, monitoring gaps, and delayed escalation can contribute to major incidents. The analysis highlights the importance of security-aware support practices in regulated environments.
This project examines the Trinity Health breach through confidentiality, integrity, availability, accountability, and patient trust. I focused on how technical weaknesses and operational decisions combine during real incidents, especially when detection and escalation are delayed.
My role
Documented the incident timeline, connected technical gaps to legal and ethical exposure, and developed recommendations around monitoring, access control, and response quality.
IT support relevance
Shows that I understand when routine support decisions have security consequences and when issues need to move beyond normal ticket handling into formal escalation.
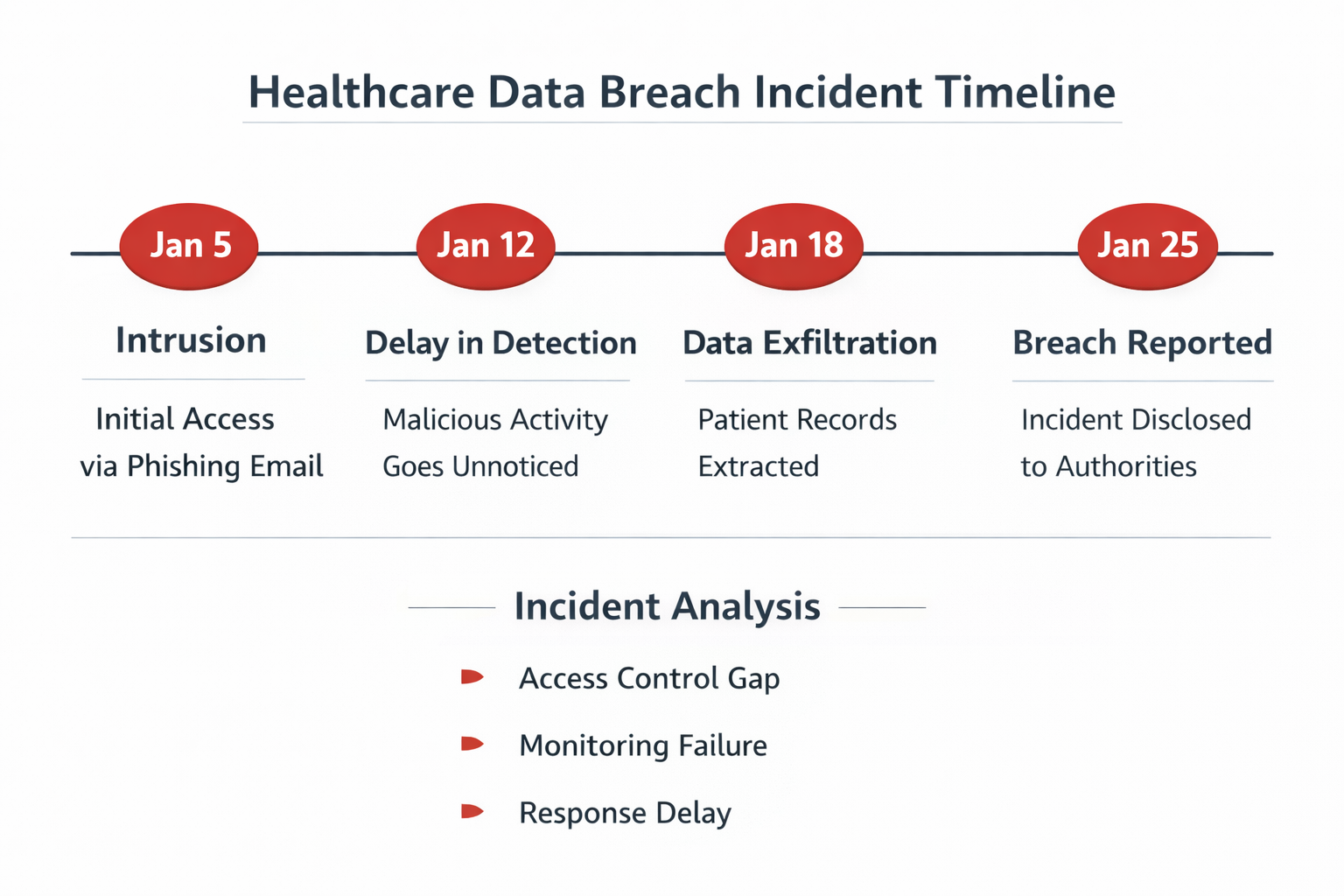
Core findings
- Unauthorized access persisted for nearly a month before detection.
- Sensitive patient data including Social Security numbers and treatment information was exposed.
- The breach raised concerns around monitoring, incident response, and patient notification quality.
- Regulatory and legal issues extended beyond compliance into ethics and trust.
Incident workflow focus
| Stage | Observed gap | Operational lesson |
|---|---|---|
| Detection | Unauthorized access remained active too long | Monitoring quality directly affects incident size |
| Response | Escalation and containment pressure increased over time | Support teams need clear criteria for when to escalate |
| Communication | Notification quality affected trust and accountability | Documentation matters during high-impact incidents |
| Recovery | Broader governance questions remained | Technical fixes alone are not enough after a breach |
Recommendations
- Improve intrusion detection and continuous monitoring.
- Use multi-factor authentication for privileged systems.
- Strengthen role-based awareness training.
- Adopt more transparent and patient-centered breach communication.
What this proves
I think this project shows that I can analyze incidents with both technical and operational judgment. It demonstrates security awareness that is useful in support roles, especially in regulated environments where access handling and escalation decisions matter.